...
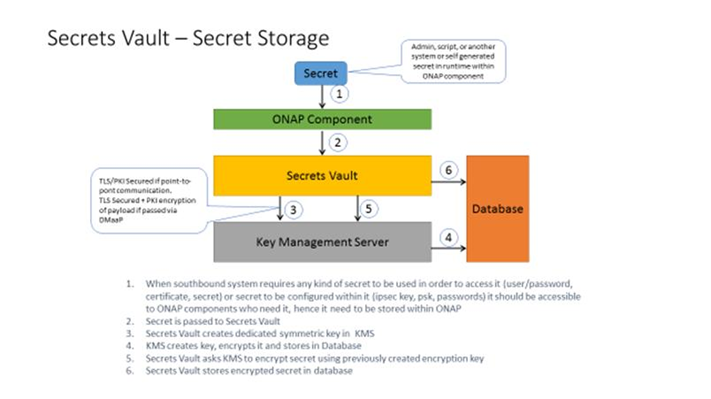
Component 1: Secrets Vault - A service that can be integrated with ONAP that provides secure storage of the credentials used by ONAP to authenticate to VNFs.
Components
1) Vault for secret storage: storage of passwords, secrets, certificates or anything else that might be used in order to access or authenticate to some system
2) Key Management Server: used to generate/manage crypro keys that are used by other parts of the system (for example Vault) and perform crypto operations (in case we don’t
want keys to leave the server)
High high level architecture approach for both components
1) External interface – for consumption by the system
2) Internal implementation interface/plugin system – to enable integration with pre-existing solutions
3) “Naïve” Native implementation – does all the stuff that required in order for system to be fully operational and secure out of box without any external systems To be used during testing/demoes or by people without hardware solutions
at place.
Use cases
Use case: provisioning SD-[W,L]AN service over already instantiated Juniper VNFs (or PNFs)
using IPsec tunnel
1) ONAP got request to service provisioning. Information includes IDs of VNFs that
service should be provisioned over
2) MSO/SA forwards request to SDN-C
3) SDN-C sends request to Secrets Vault to retrieve credentials to abovementioned VNFs by their ID
4) Secrets Vault sends back to SDN-C credentials
5) SDN-C generates pre-shared key for IPsec tunnel provisioning
6) SDN-C sends to Secrets Vault request to store pre-shared key
7) SDN-C using retrieved credentials connects via SSH to VNFs and configures
IPsec tunnel using PSK
Use case extension: at later timeframe SD-[W,L]an service is extended to new branch where VNF needs
to be instantiated
1) ONAP got request to service provisioning.
2) MSO instantiates new VNF and passes it to APP-C for initial configuration
3) APP-C generates random user name and password (aka credentials)
4) APP-C sends request to Secrets Vault to store credentials by VNF ID
5) APP-C configures new VNF to use new credentials
6) APP-C notifies MSO that it finished
7) MSO/SA forwards request to SDN-C
8) SDN-C sends request to Secrets Vault to retrieve credentials to abovementioned VNF by his ID
9) Secrets Vault sends back to SDN-C credentials
10) SDN-C sends request to Secrets Vault to retrieve pre shared IPsec key for IPsec tunnel
11) Secrets Vault sends back IPsec key
12) SDN-C using retrieved credentials connects via SSH to VNFs and configures IPsec tunnel using retrieved PSK
13) Everybody happy and everything is secured
- OpenStack’s Barbican: specific to OpenStack, not a mature service
- Various commercial services such as LastPass
...