In this page, we will describe how to configure AAF's bath_config.csv file based on AAF's role, user, perm setup.
Key URLs
OpenDaylight AAA concept: https://docs.opendaylight.org/projects/aaa/en/latest/dev-guide.html
Base64 encode and decode: https://www.base64decode.org/
APPC api frontend: https://<rancher ip>:30230/apidoc/explorer/index.html
AAF GUI CLI: https://<rancher ip>:31113/gui/cui
APPC permissions outlines
| user in AAA | user in AAF | permission and role |
|---|---|---|
| admin | appc@appc.onap.org | Admin right for any writable/readable paths access |
| jolokiaall | demo@people.osaaf.org | /jolokia path writable/readable access |
| restall | aaf_admin@people.osaaf.org | /apidoc AND /restconf paths writable/readable access |
| odlro | mmmanger@people.osaaf.org | readonly access |
Create AAA users using TokenAuthRealm IdM policy
download the aaa_user tar file:
untar aaa_user.tar in k8s env. the tar file contains:
- aaa_users.sh : the script creating AAA users.
- user1.json: jolokiaall user
- user2.json: restall user
- user3.json: odlro user
the default password for each user is the same user's name. In order to change password, please follow the steps below:
- recreate base64 encrypted entry in bath_confg.csv file
For example, if you want to change password for "jolokiaall" user to "jolokiaall123!":
goto https://www.base64decode.org/, click "Encode" on the top of function selection. Put "jolokiaall:jolokiaall123!" then click ">ENCODE<" button.
copy & paste the string: "am9sb2tpYWFsbDpqb2xva2lhYWxsMTIzIQ==" replace the string "am9sb2tpYWFsbDpqb2xva2lhYWxs" on line #4 in the bath_config.csv file.
The bath_confg.csv file is under APPC helm chart: oom/kubernetes/appc/resources/config/appc/opt/onap/appc/data/properties
redeploy APPC helm chart in ONAP k8s env.
- replace the password in the AAA user json file:
Continue the example above:
replace "jolokiaall123!" in user1.json
run ./aaa_users.sh
Setup AAA's role, perm via AAF GUI CLI
using AAF GUI CLI to setup AAA role perm individually
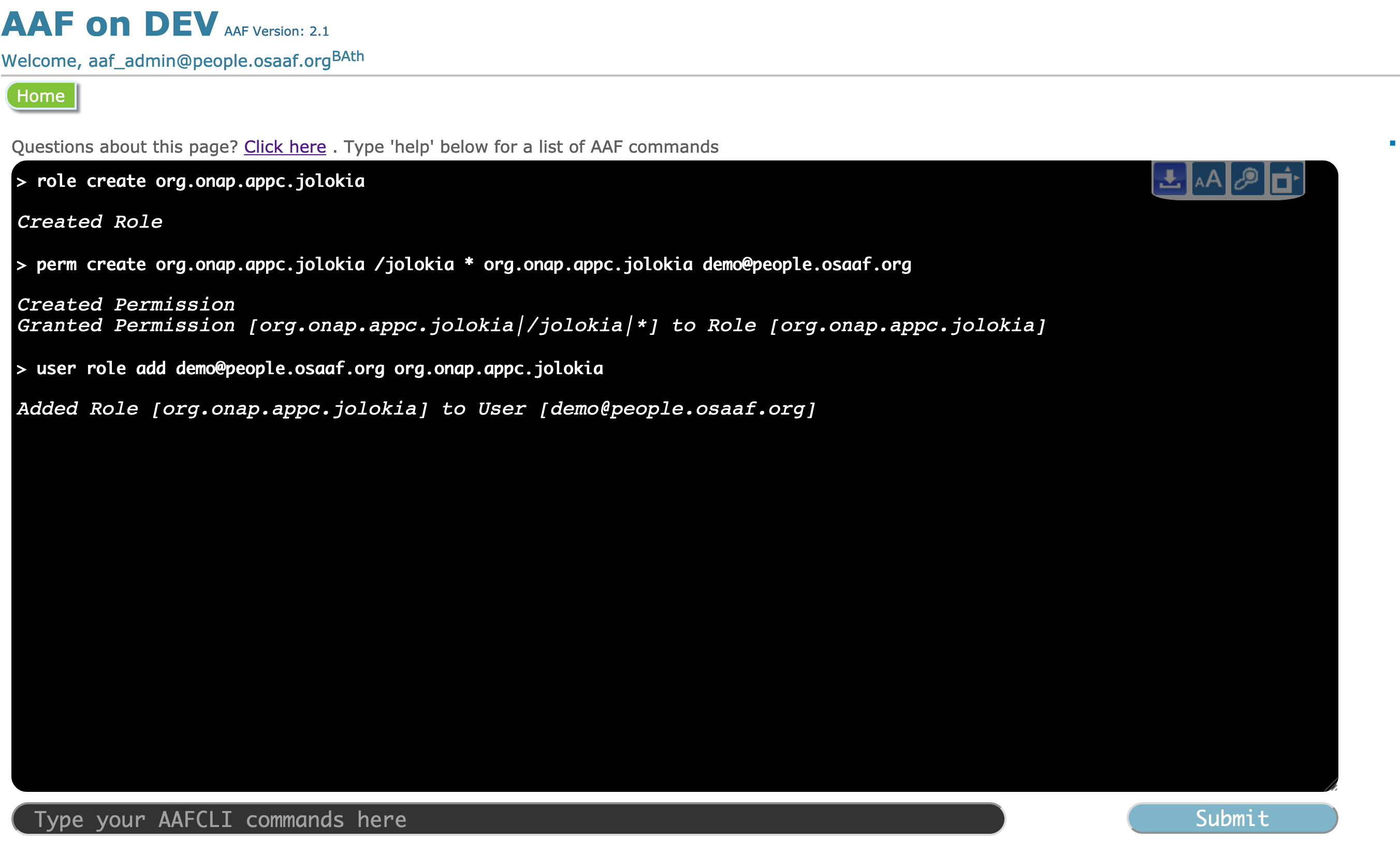
- for "jolokiaall" user: run the following AAF commands:
role create org.onap.appc.jolokia perm create org.onap.appc.jolokia /jolokia * org.onap.appc.jolokia demo@people.osaaf.org user role add demo@people.osaaf.org org.onap.appc.jolokia
test #1 jolokiaall user for /jolokia path below. jolokiaall should get /jolokia perm
curl -u "jolokiaall:jolokiaall" -k -X GET -s -H "Content-type:application/json" https://${IP}:30230/jolokia/list | python -mjson.tool
test #2 jolokiaall user for other path: /auth below. 401 Error returned
curl -u "jolokiaall:jolokiaall" -k -X GET -s -H "Content-type:application/json" https://${IP}:30230/auth/v1/users
- for "restall" user: run the following AAF commands:
role create org.onap.appc.restconf perm create org.onap.appc.restconf /apidoc * org.onap.appc.restconf aaf_admin@people.osaaf.org perm create org.onap.appc.restconf /restconf * org.onap.appc.restconf aaf_admin@people.osaaf.org user role add aaf_admin@people.osaaf.org org.onap.appc.restconf
The bug has been created AAF-987 - Getting issue details... STATUS once the issue has been resolved. will continue updating this wiki page. (9/26/2019 - Takamune Cho )