1. Introduction
The ONAP Security Best Practices is a list of Best Practices recommended by the ONAP sub-committee. These best practices have the following states:
- Draft: It is still under discussion in the ONAP security sub-committee
- Recommended: It is recommended by the security sub-committee but not yet approved by the TSC
- Approved: It is approved by the TSC.
2. CII Badging Program.
Status: Approved
Best Practice:
It is recommended that the ONAP projects are certified as part of the CII badging program. A gold badge is recommended, however the basic passing badge is the starting point.
This is currently being introduced slowly with 2 projects undergoing certification.
•Basic introduction can be found here: https://github.com/coreinfrastructure/best-practices-badge/blob/master/doc/criteria.md
•Silver/Gold criteria can be found here: https://github.com/coreinfrastructure/best-practices-badge/blob/master/doc/other.md
3. Credential Protection and Management
Status: Draft
Best Practice:
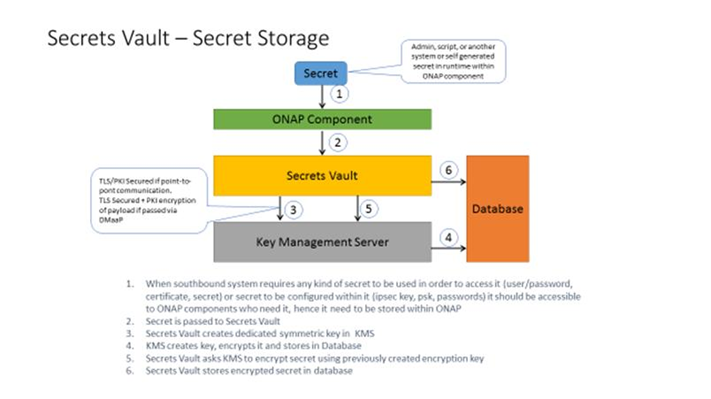
ONAP requires two components to improve the security of credentials used in orchestration.
- a secrets vault to store credentials used by ONAP
- a process to instantiate credentials
Component 1: Secrets Vault - A service that can be integrated with ONAP that provides secure storage of the credentials used by ONAP to authenticate to VNFs.
- OpenStack’s Barbican: specific to OpenStack, not a mature service
- Various commercial services such as LastPass
Recommendation: ONAP should provide a reference implementation of a secrets vault service as an ONAP project.
Next Steps:
- Find a project lead for a reference implementation.
Component 2: A process to provision ONAP instances with credentials. These credentials may be used for interprocess communication (e.g., APPC calling A&AI) or for ONAP configuring VNFs.
Automatic provisioning of certificates and credentials to ONAP components: AAF can provision certificates. ECOMP DCAE is currently using AAF to provision certificates.
Next steps:
- Work with the AAF team to include this functionality in Release 2. It is important to understand that the AAF solution depends on the CA supporting the SCEP protocol.
- Enhance AAF to provision userIDs & passwords to ONAP instances and VNFs. Most VNFs only support userID/password authentication today. ETSI NFV SEC may issue a spec in the future on a more comprehensive approach to using PKI for NFV which can be visited by ONAP SEC when released. Steve is working on this right now but doesn’t know when he’ll be done.
4. Static Code Scans
Status: Draft
Best Practice:
Tools that have been assessed: Coverity Scan (LF evaluation), HP Fortify (AT&T evaluation), Checkmarx (AT&T evaluation), Bandit (AT&T evaluation)
Prelimary Decision: Coverity Scan https://scan.coverity.com/
Description: Coverity Scan is a service by which Synopsys provides the results of analysis on open source coding projects to open source code developers that have registered their products with Coverity Scan. Coverity Scan is powered by Coverity® Quality Advisor. Coverity Quality Advisor surfaces defects identified by the Coverity Static Analysis Verification Engine (Coverity SAVE®). Synopsys offers the results of the analysis completed by Coverity Quality Advisor on registered projects at no charge to registered open source developers.
Current Activity: In conversations with Coverity to understand the definition of “project” – does it refer to ONAP or the projects under an ONAP release to ensure that the limitation on free scans does not lead to bottlenecks in submissions and commits.
Open Source use: 4000+ open source projects use Coverity Scan
Frequency of builds:
Up to 28 builds per week, with a maximum of 4 builds per day, for projects with fewer than 100K lines of code
Up to 21 builds per week, with a maximum of 3 builds per day, for projects with 100K to 500K lines of code
Up to 14 builds per week, with a maximum of 2 build per day, for projects with 500K to 1 million lines of code
Up to 7 builds per week, with a maximum of 1 build per day, for projects with more than 1 million lines of code
Once a project reaches the maximum builds per week, additional build requests will be rejected. You will be able to re-submit the build request the following week.
Languages supported: C/C++, C#, Java, Javascript, Python, Ruby