Oauth2 Proxy is used to provide the redirection / cookie check in order to enforce JWT presence even via web browser
General concept:
https://medium.com/@senthilrch/api-authentication-using-istio-ingress-gateway-oauth2-proxy-and-keycloak-part-2-of-2-dbb3fb9cd0d0
https://discuss.istio.io/t/how-to-implement-istio-authorization-using-oauth2-and-keycloak/13707
Add Oauth2-Proxy client to Keycloak-Realm:
https://discuss.istio.io/t/how-to-implement-istio-authorization-based-on-keycloak-user-role/13716
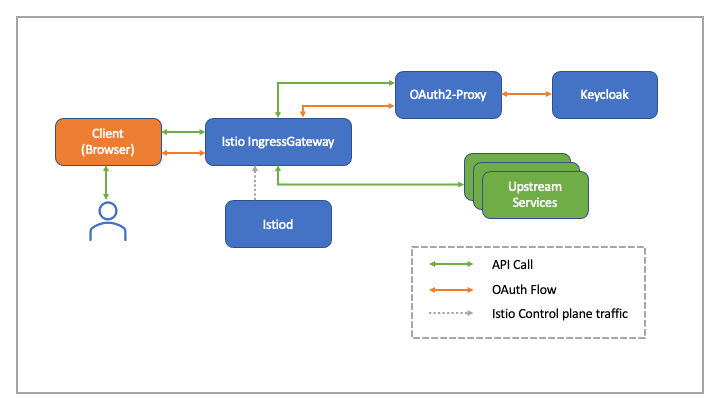
General Architecture
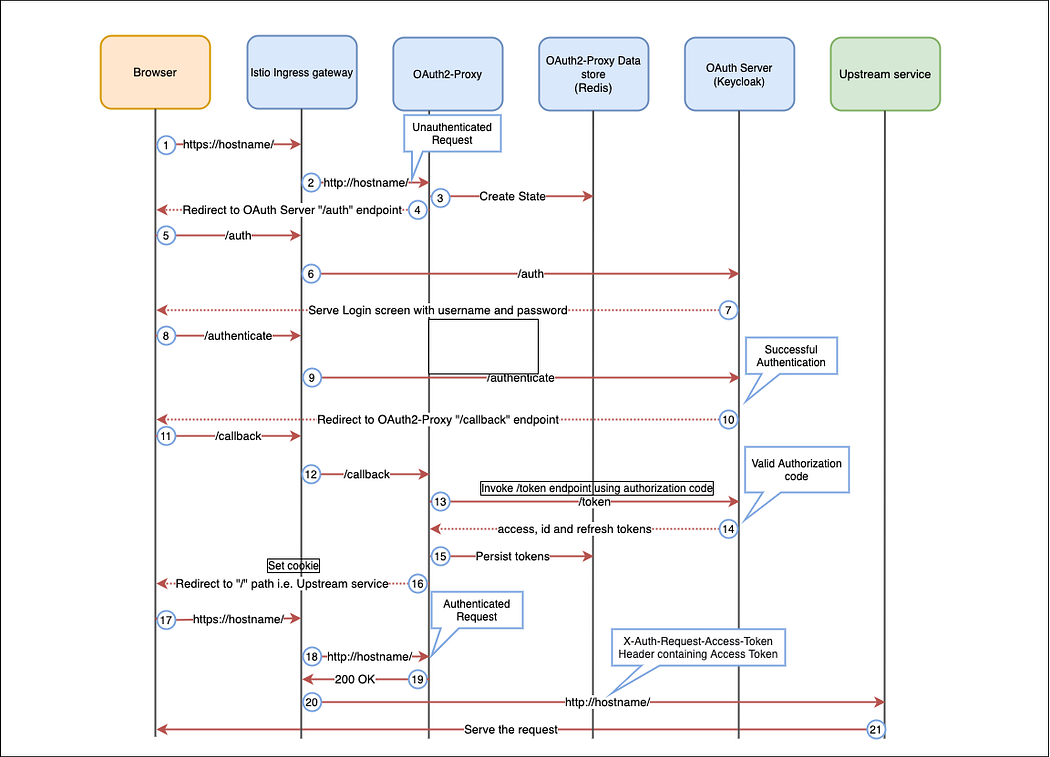
Authentication Message Flow
- User enters the hostname of the server in the browser. The request is sent to the Istio Ingress Gateway.
- Ingress Gateway forwards the request to OAuth2-Proxy for authentication.
- The OAuth2-Proxy determines the request is not authenticated yet. It creates state in its Redis Key value store.
- OAuth2-Proxy redirects the browser to /auth endpoint of Keycloak.
- The browser sends a request to the /auth endpoint which is sent to the Ingress Gateway.
- Ingress Gateway forwards the request to Keycloak
- Keycloak serves the login screen containing fields for Username and Password.
- User enters Username and Password and submits the form. The browser sends a request to the /authenticate endpoint of Keycloak. The request is sent to the Ingress Gateway.
- Ingress Gateway forwards the request to Keycloak, which verifies the credentials of the user and generates an Authorization code.
- Keycloak then redirects the browser to the /callback endpoint of OAuth2-Proxy with Authorization code as query parameter in the URL.
- The browser sends a request to the /callback endpoint which is sent to the Ingress Gateway.
- Ingress Gateway forwards the request to OAuth2-Proxy
- OAuth2-Proxy invokes the /token endpoint of Keycloak using the Authorization code.
- Keycloak validates the Authorization code and responds back with access token, id token and refresh token
- OAuth2-Proxy persists the tokens in its Redis Key value store.
- OAuth2-Proxy redirects the browser to the original url requested by the user i.e. hostname. It instructs the browser to store a cookie with a specific key configured in OAuth2-Proxy
- The browser sends a request to hostname, this time the request will contain the cookie header containing cookie that was sent by OAuth2-Proxy. The request is sent to the Ingress Gateway.
- Ingress Gateway forwards the request to OAuth2-Proxy to verify if the request is authenticated properly
- OAuth2-Proxy responds back with a HTTP 200 OK response that contains the access token in “X-Auth-Request-Access-Token” header
- Ingress Gateway perform API Access control checks. It then forwards the request to upstream service with “X-Auth-Request-Access-Token” header in it.
- The upstream service serves the request.